Lab 1-1
Description
This lab uses the files Lab01-01.exe and Lab01-01.dll. Use the tools and techniques described in the chapter to gain information about the files and answer the questions below.
- Upload the files to http://www.VirusTotal.com/ and view the reports. Does either file match any existing antivirus signatures?
- When were these files compiled?
- Are there any indications that either of these files is packed or obfuscated? If so, what are these indicators?
- Do any imports hint at what this malware does? If so, which imports are they?
- Are there any other files or host-based indicators that you could look for on infected systems?
- What network-based indicators could be used to find this malware on infected machines?
- What would you guess is the purpose of these files?
Solution
Lab01-01.dll
-
VirusTotal results shows us that the file could be a trojan from the skeeyah family of malware.
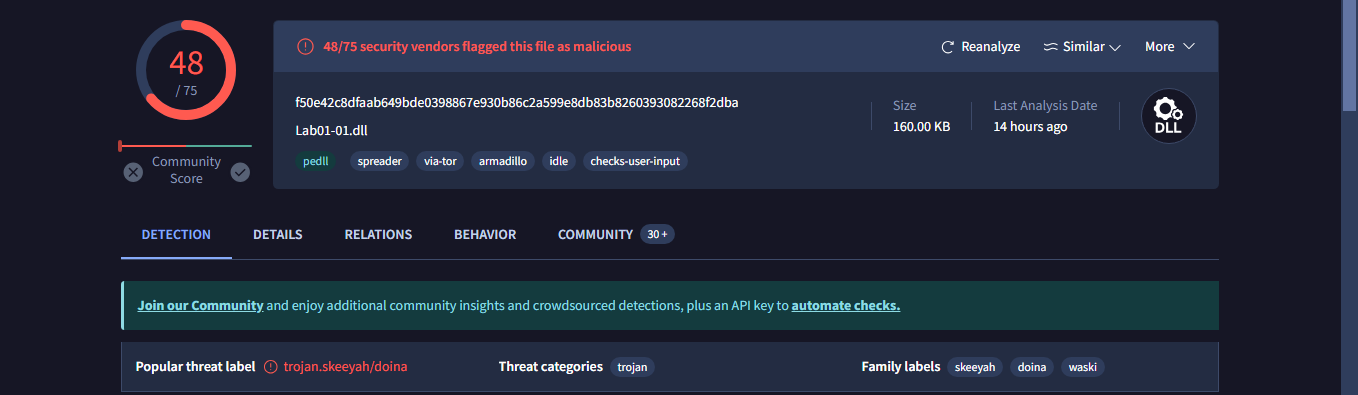
The DLL here matches nearly 48 vendors as malicious. -
The file was compiled at
2010/12/19 Sunday 16:16:38 UTC. -
PEiD shows us that the file was compiled and linked by the Microsoft Visual C++ 6.0 DLL.
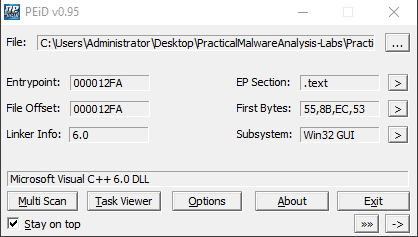
In addition to this, The difference between the Virtual Size and the Size of Raw Data of the.textsection isn’t that big, indicating that this DLL is not obfuscated.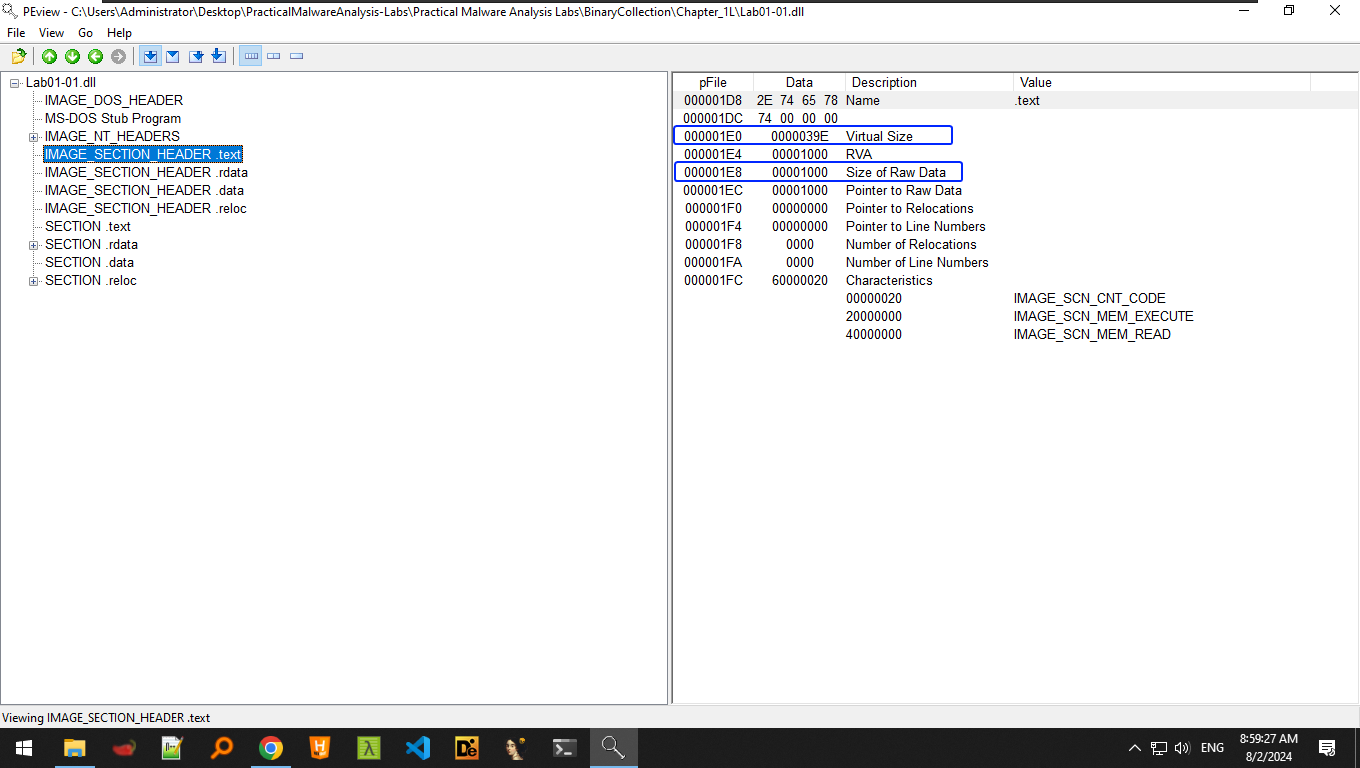
-
It does import the WS2_32.DLL library which is commonly used for socket connections and networking. At first glance, it uses ordinals to call these functions, so names are not visible at first glance. Dependency Walker shows us that the DLL imports functions:
closesocket(),connect(),recv(),send()which indicates that this DLL connects to a server, sending and receiving data, this matches correctly with the reports from VirusTotal as shown above. -
Looking on the strings of the DLL, we find nothing for host based indicators.
-
We do find an IP address within the DLL:
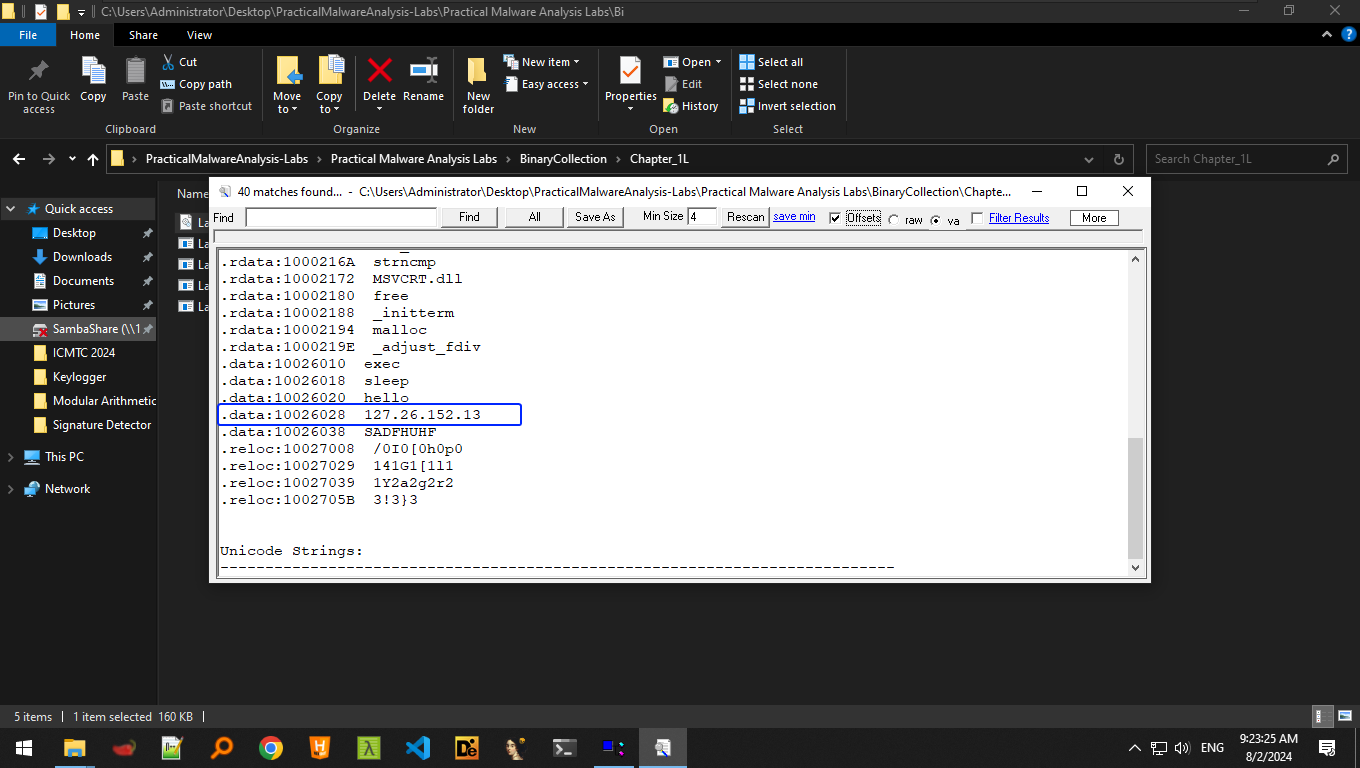 This can be a solid indicator of this malware, so we must be on the lookout for packets sent/received to this IP address.
This can be a solid indicator of this malware, so we must be on the lookout for packets sent/received to this IP address. -
The DLL mainly serves as a backdoor to a C2 server.
Lab01-01.exe
- VirusTotal shows us that the exe is malicious by 58 vendors.
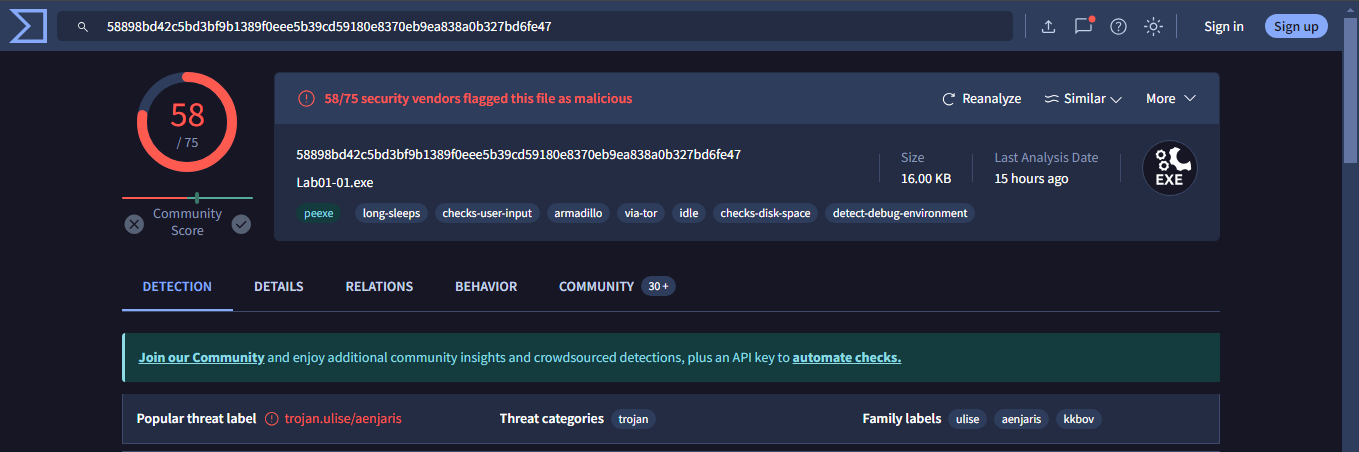 VirusTotal also shows that this malware belongs to the ulise trojan family.
VirusTotal also shows that this malware belongs to the ulise trojan family. - This file was compiled at
2010/12/19 Sun 16:16:19 UTC, compiled within a minute timespan of its DLL. - This file was compiled by MS Visual C++ 6.0.
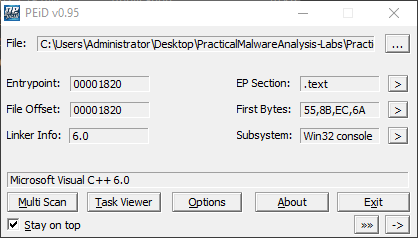 The size difference between the Virtual Size and the Size of Raw Data of the
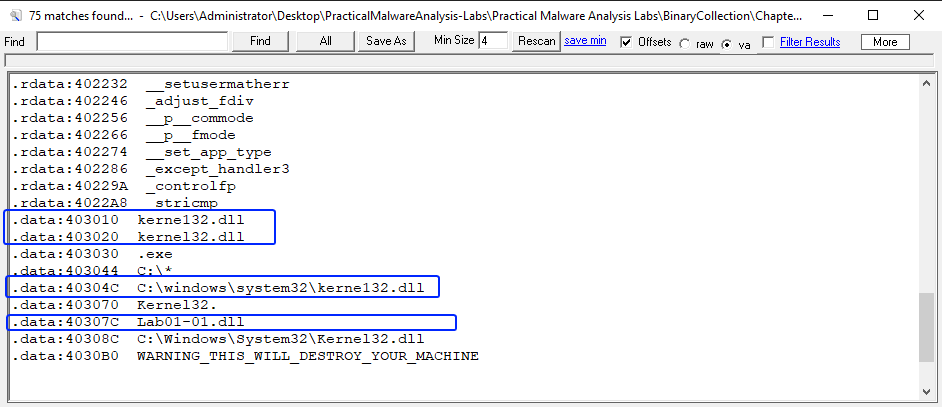
The size difference between the Virtual Size and the Size of Raw Data of the .textsection is not huge, we can conclude that the exe is not obfuscated. - This file imports the kernel32.dll file, but what’s interesting is that it imported two functions that are used to find files.
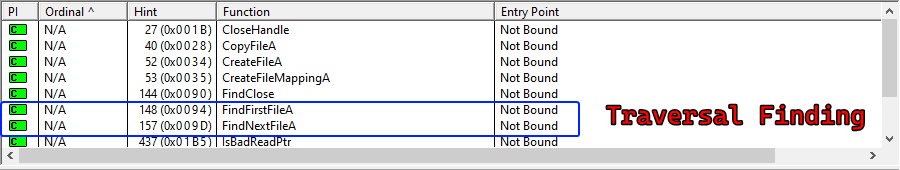
- We find two host based indicators of interest: Lab01-01.dll and kerne132.dll (Attempting to masquerade as the real kernel32.dll)
- We don’t exactly find a network based indicator with the exe alone, although it exists within the DLL that it uses.
- The exe seems to install the Lab01-01.dll file and the fake kerne132.dll and checks if they have been installed or not using the
FindFirstFileA()andFindNextFileA().
We can conclude that the DLL is a backdoor and the exe is used to installer that backdoor.
Lab 1-2
Description
Analyze the file Lab01-02.exe.
Questions:
- Upload the Lab01-02.exe file to http://www.VirusTotal.com/. Does it match any existing antivirus definitions?
- Are there any indications that this file is packed or obfuscated? If so, what are these indicators? If the file is packed, unpack it if possible.
- Do any imports hint at this program’s functionality? If so, which imports are they and what do they tell you?
- What host- or network-based indicators could be used to identify this malware on infected machines?
Solution
- 56 vendors mark this file as malicious, it is of the same family as Lab01-01.exe.
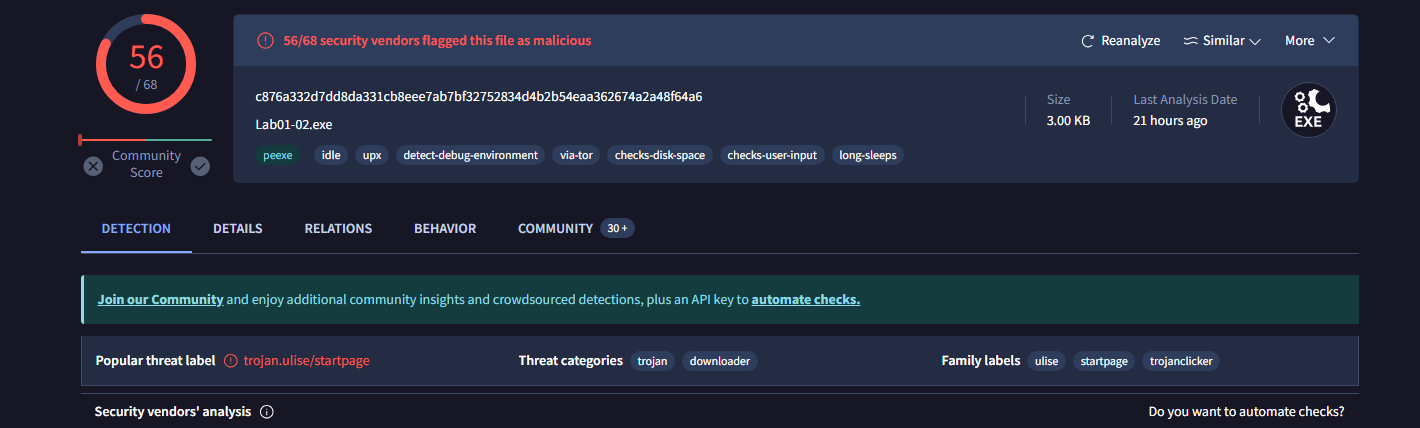 We also notice that it has a
We also notice that it has a upxtag on it which indicates that this file could be packed, it also has a threat category of being a downloader. - This file is indeed packed by the
upxpacker, as shown by PEiD.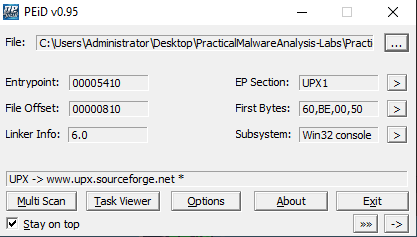
We can unpack the file using theupxcmd utility.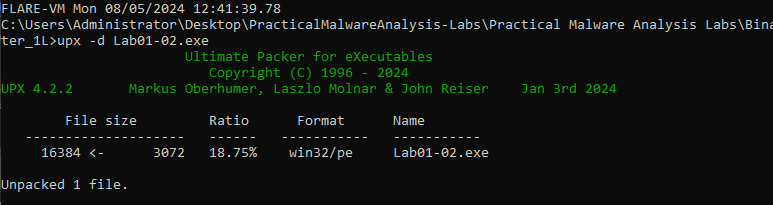
- Using the PEstudio tool, we find that the sample imports the following functions:
We see WININET.DLL which operates on the internet, specifically OSI Layer 7 protocols, such as HTTP, FTP, etc…
Checking the import list of the exe we find a few interesting functions: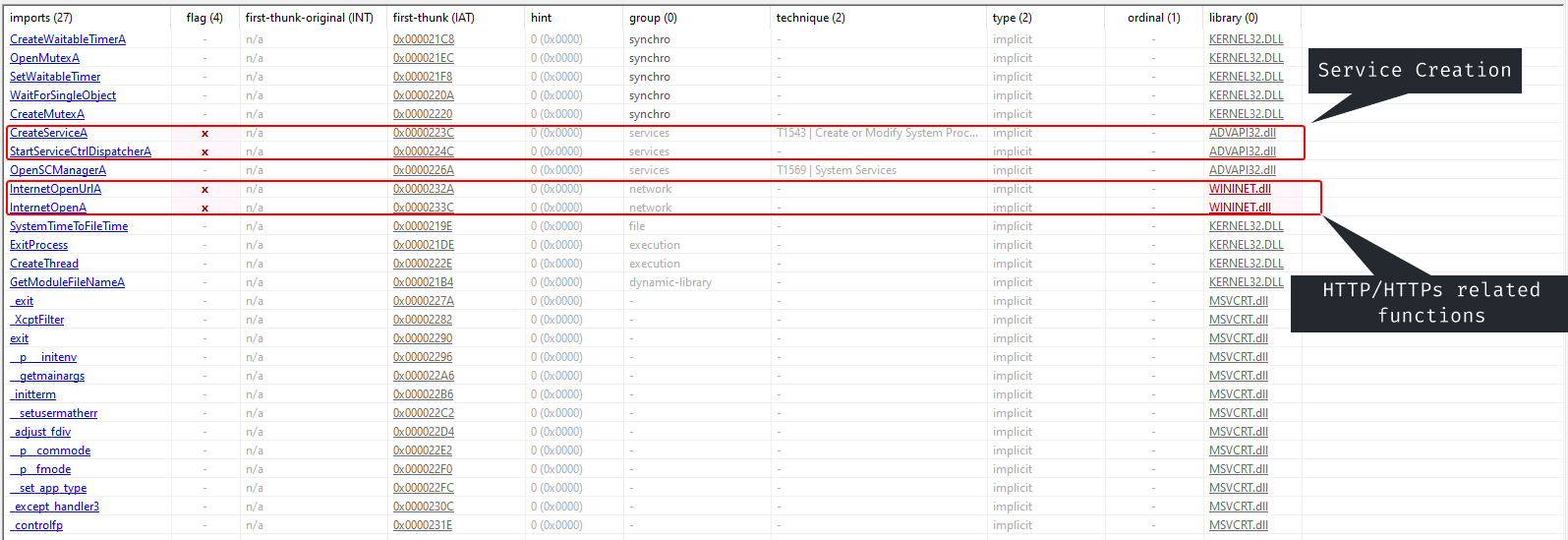
We notice here that the malware could install itself as a windows service, and it attempts to communicate through the internet by an FTP or HTTP connection. - Checking the strings of the program we find a few interesting strings:
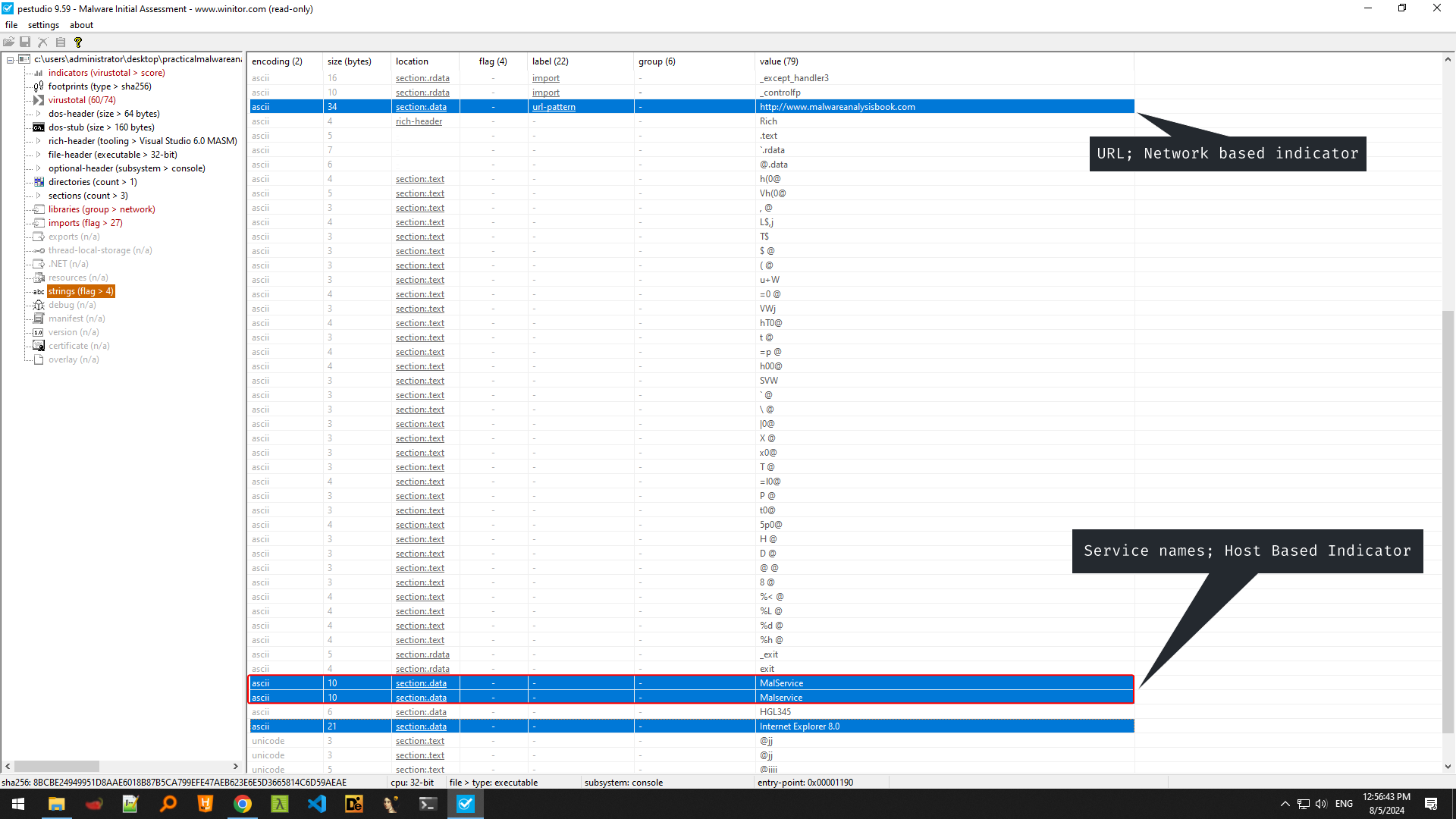 We find a URL; which could be the server that the malware attempts to communicate to. And the service name that the malware uses when it installs itself onto the system.
We find a URL; which could be the server that the malware attempts to communicate to. And the service name that the malware uses when it installs itself onto the system.
Lab 1-3
Description
Analyze the file Lab01-03.exe.
Questions
- Upload the Lab01-03.exe file to http://www.VirusTotal.com/. Does it match any existing antivirus definitions?
- Are there any indications that this file is packed or obfuscated? If so, what are these indicators? If the file is packed, unpack it if possible.
- Do any imports hint at this program’s functionality? If so, which imports are they and what do they tell you?
- What host- or network-based indicators could be used to identify this malware on infected machines?
Solution
- 68 vendors mark this file as malicious, it has the flags of trojan spyware.
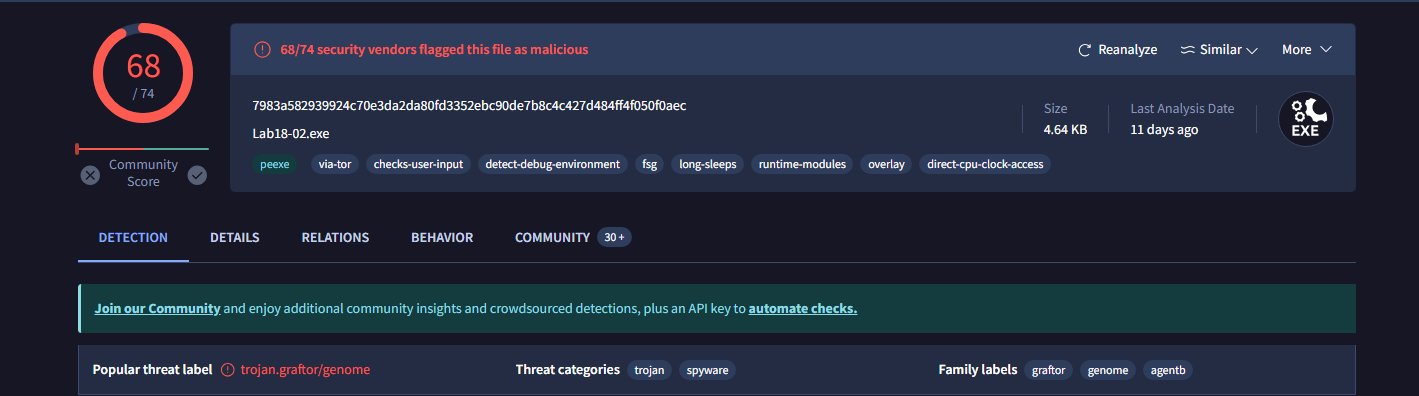
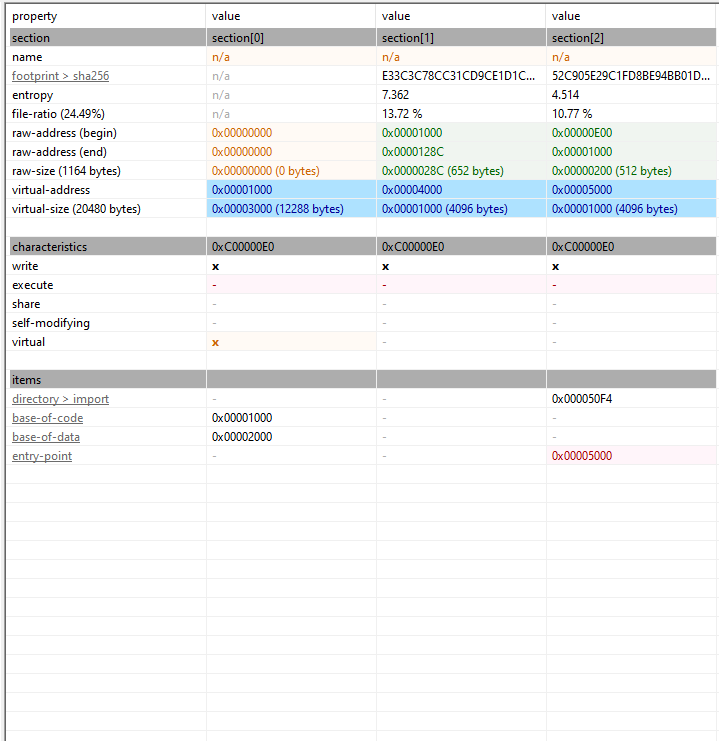
- This programs has only two imports, and three sections that have no names is an indicative sign of a packed file. We also notice that each section has 0 size of raw data and its virtual size is
0x1000, This sample is packed byFSG 1 -> dulet/xt
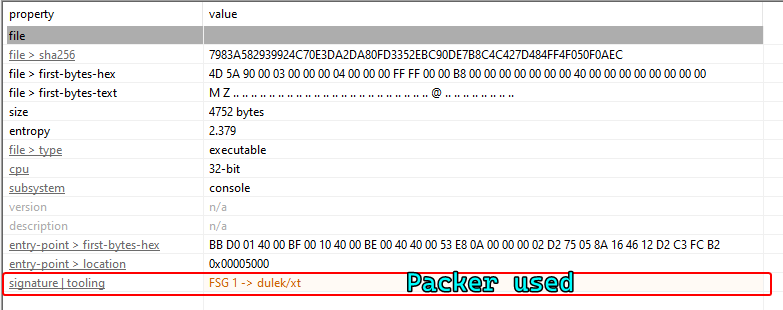

- As the program is packed by FSG, we can’t as of writing this unpack the file.
- The file is packed, we can’t make sure of its functionality as of yet.
Lab 1-4
Description
Questions
- Upload the Lab01-04.exe file to http://www.VirusTotal.com/. Does it match any existing antivirus definitions?
- Are there any indications that this file is packed or obfuscated? If so, what are these indicators? If the file is packed, unpack it if possible.
- When was this program compiled?
- Do any imports hint at this program’s functionality? If so, which imports are they and what do they tell you?
- What host- or network-based indicators could be used to identify this malware on infected machines?
- This file has one resource in the resource section. Use Resource Hacker to examine that resource, and then use it to extract the resource. What can you learn from the resource?
Solution
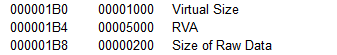
- This sample is flagged by 66 vendors, it has the tags of a dropper/downloader trojan.
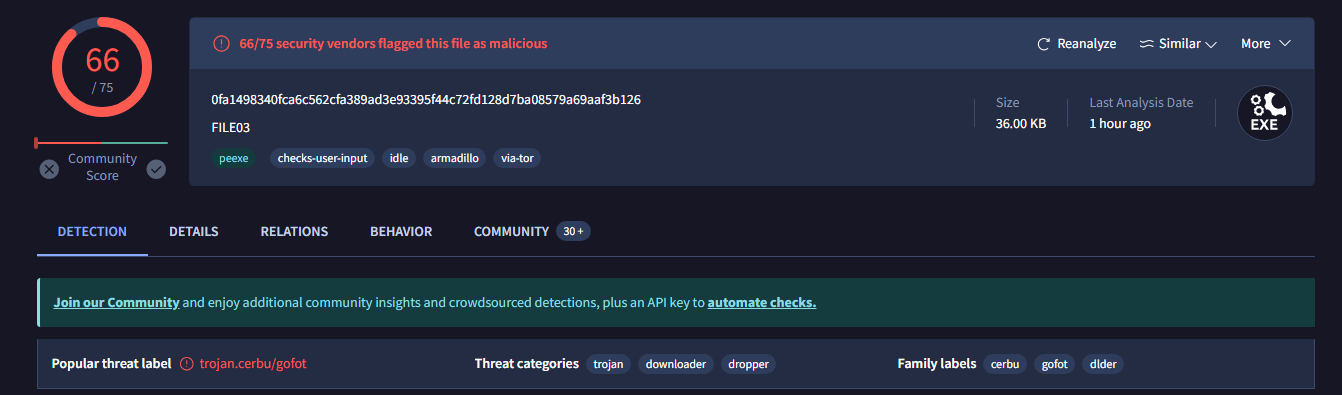
- This file is unpacked.
- This program was compiled at
Fri Aug 30 22:26:59 2019 (UTC) - The sample has a few interesting imports that are used for process injection, we also notice that the sample has an executable in the
.rsrcsection, this could be the executable that it attempts to inject.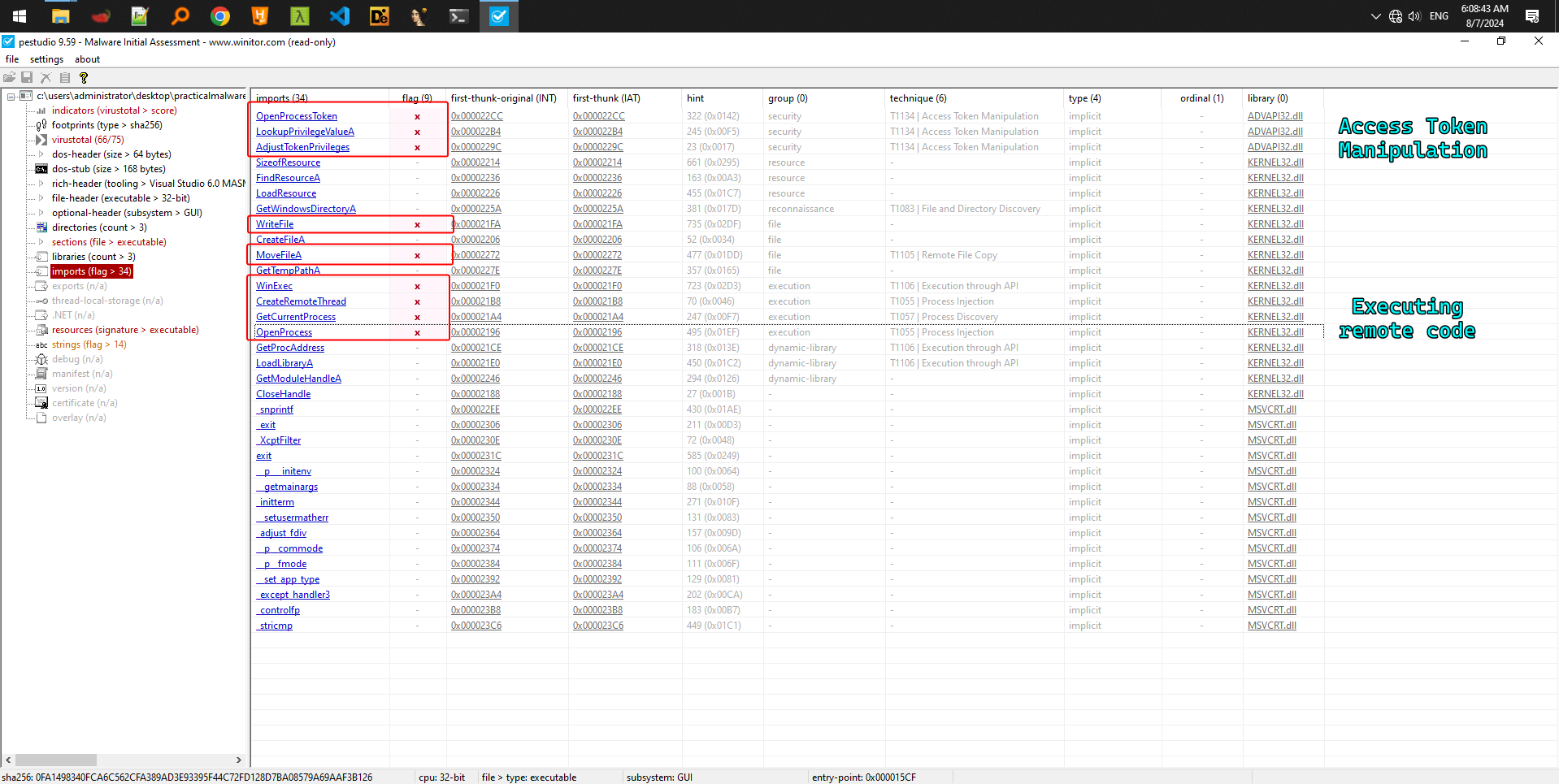
- We have a few host indicators and 1 network indicator, this sample attempts to masquerade as a “Windows Update” executable.
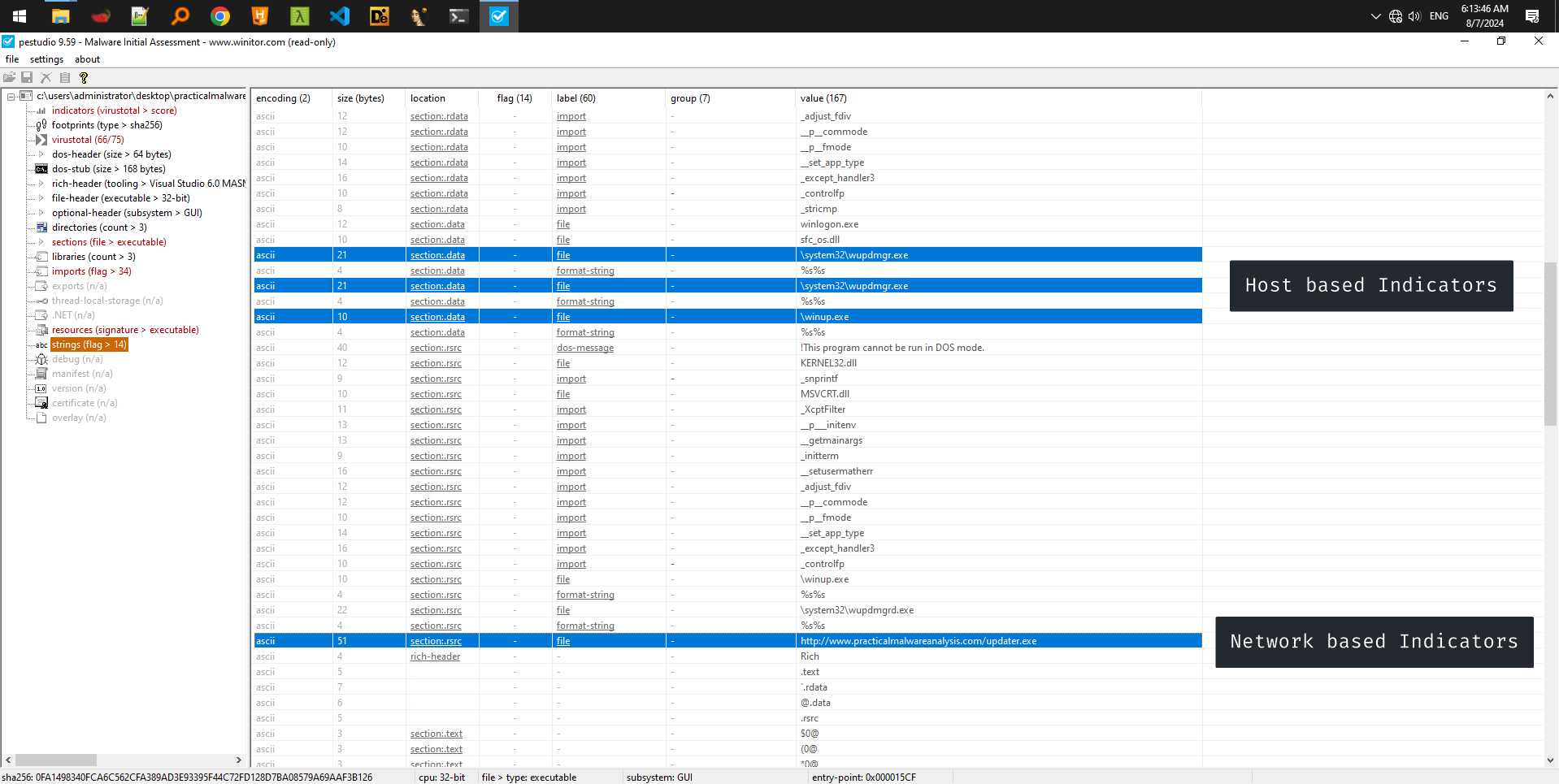
- We have a resource named “BIN” in the original sample, we can export this sample as a bin file and analyze it: We notice that this malware has a few interesting exports
URLDownloadToFile()andWinExec(): So the injected binary basically downloads a file from the internet, writes it to a file and then executes it usingWinExec()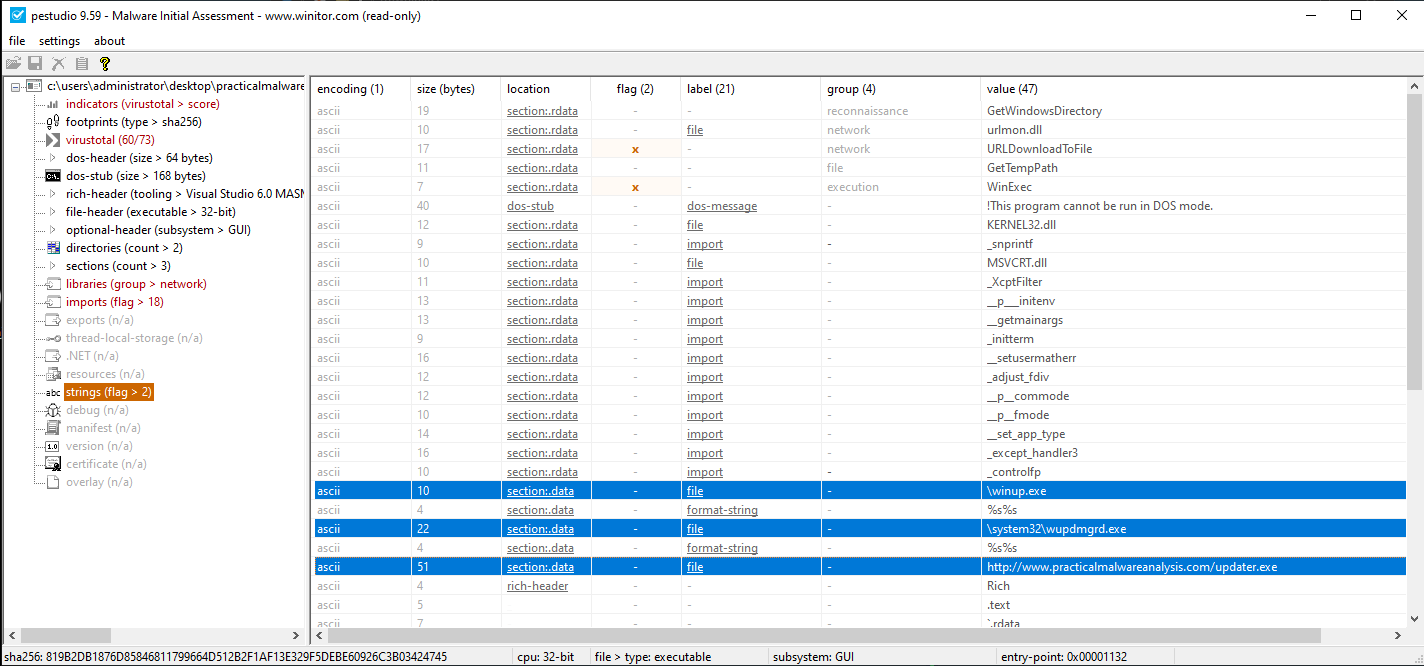
We also notice that it has the same indicators as the main sample.
Final Conclusion: The main sample is only but a process injector that injects the malicious binary resource into processes, and then that malicious binary resource downloads its malicious “updater.exe” into your system and then executes it usingWinExec()
Next lab: Lab 3