Description
Analyze the malware found in the file Lab05-01.dll using only IDA Pro.
The goal of this lab is to give you hands-on experience with IDA Pro. If you’ve already worked with IDA Pro, you may choose to ignore these questions and focus on reverse-engineering the malware.Questions
- What is the address of DllMain?
- Use the Imports window to browse to gethostbyname. Where is the import located?
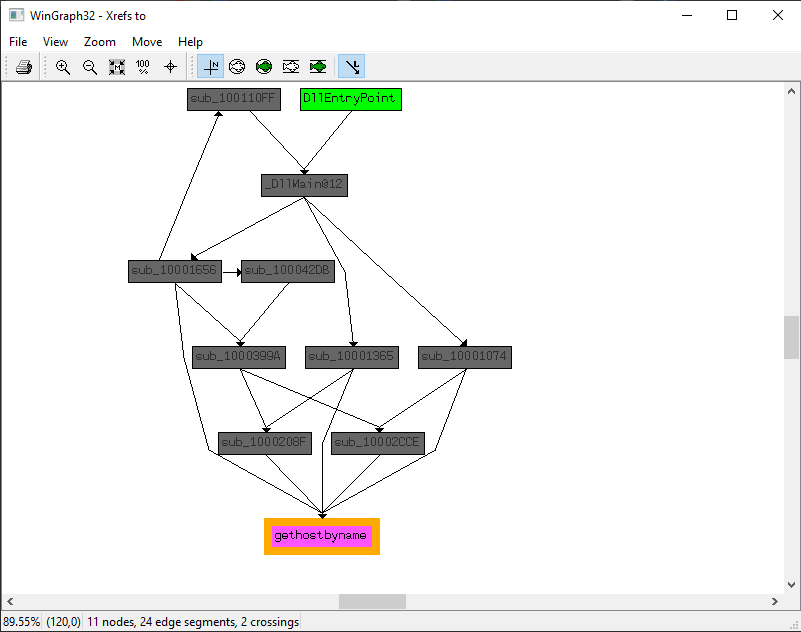
- How many functions call gethostbyname?
- Focusing on the call to gethostbyname located at 0x10001757, can you figure out which DNS request will be made?
- How many local variables has IDA Pro recognized for the subroutine at 0x10001656?
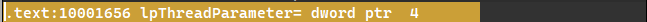
- How many parameters has IDA Pro recognized for the subroutine at 0x10001656?
- Use the Strings window to locate the string \cmd.exe /c in the disassembly. Where is it located?
- What is happening in the area of code that references \cmd.exe /c?
- In the same area, at 0x100101C8, it looks like dword_1008E5C4 is a global variable that helps decide which path to take. How does the malware set dword_1008E5C4? (Hint: Use dword_1008E5C4’s cross-references.)
- A few hundred lines into the subroutine at 0x1000FF58, a series of comparisons use memcmp to compare strings. What happens if the string comparison to robotwork is successful (when memcmp returns 0)?
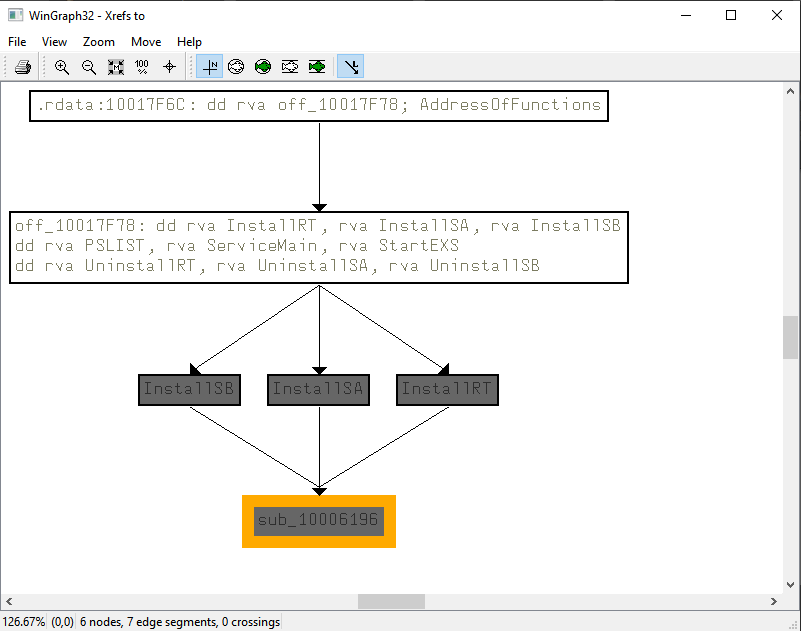
- What does the export PSLIST do?
- Use the graph mode to graph the cross-references from sub_10004E79. Which API functions could be called by entering this function? Based on the API functions alone, what could you rename this function?
- How many Windows API functions does DllMain call directly? How many at a depth of 2?
- At 0x10001358, there is a call to Sleep (an API function that takes one parameter containing the number of milliseconds to sleep). Looking backward through the code, how long will the program sleep if this code executes?
- At 0x10001701 is a call to socket. What are the three parameters? 108 Chapter 5
- Using the MSDN page for socket and the named symbolic constants functionality in IDA Pro, can you make the parameters more meaningful? What are the parameters after you apply changes?
- Search for usage of the in instruction (opcode 0xED). This instruction is used with a magic string VMXh to perform VMware detection. Is that in use in this malware? Using the cross-references to the function that executes the in instruction, is there further evidence of VMware detection?
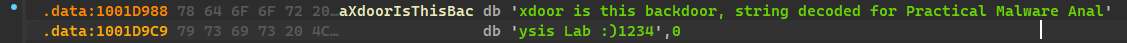
- Jump your cursor to 0x1001D988. What do you find?
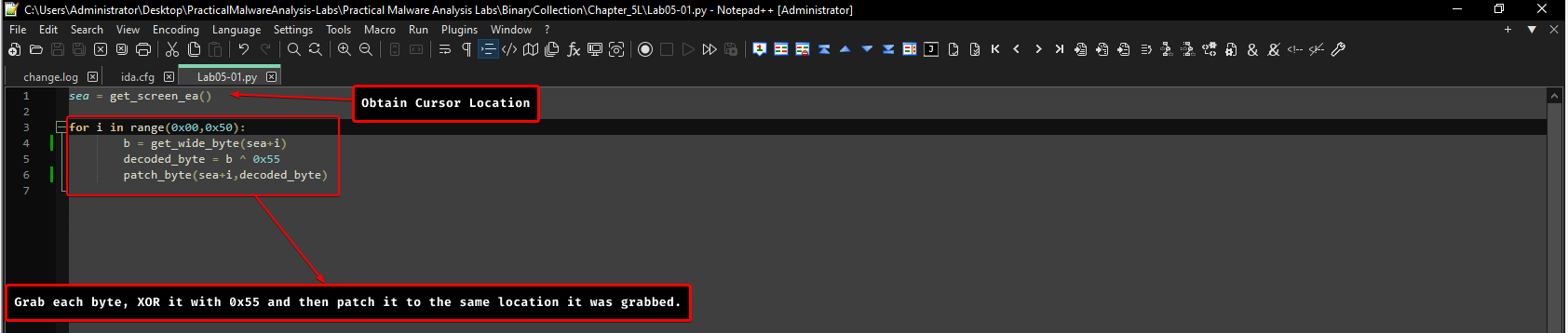
- If you have the IDA Python plug-in installed (included with the commercial version of IDA Pro), run Lab05-01.py, an IDA Pro Python script provided with the malware for this book. (Make sure the cursor is at 0x1001D988.) What happens after you run the script?
- With the cursor in the same location, how do you turn this data into a single ASCII string?
- Open the script with a text editor. How does it work?
DllMainis located at0x1000d02e.gethostbynameis located at0x100163cc.- 5 functions call
gethostbynameusing thexref tograph.
- The URL called is
pics.praticalmalwareanalysis.com - For the subroutine at
0x10001656, it has 23 variables.
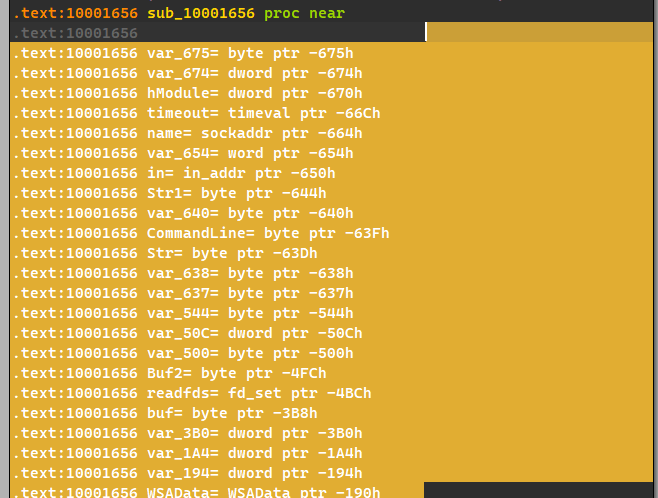
- For the subroutine at
0x10001656, we only have 1 parameter.
- It is located in the
xdoors_dsection at address0x10095b34.

- This area of code appears to be interacting with sockets, sending and receiving data, which means it could be a reverse shell.
- The malware sets this global variable based off the OS’s version using
GetVersionExA(), this function attempts to check if the OS is an NT based OS, and from there figures out which command interpreter to be used: command.exe (for Win 9x) or cmd.exe for Windows NT based OSes. - We send both the keys located
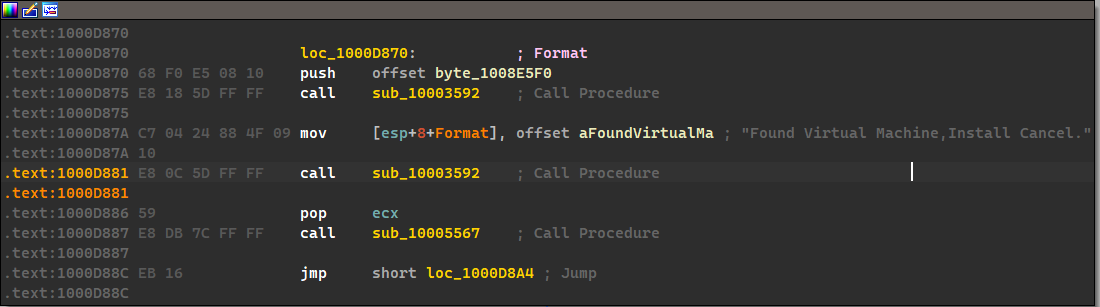
SOFTWARE\Microsoft\Windows\CurrentVersionnamedWorkTimesandWorkTimethrough the reverse shell. - As the name stands, this export attempts to list out all the processes within the OS, may it be an NT based OS or not, it uses process snapshots and traverses through them to find the given process, then sends them over the network.
- These many functions can be called when this function is called:
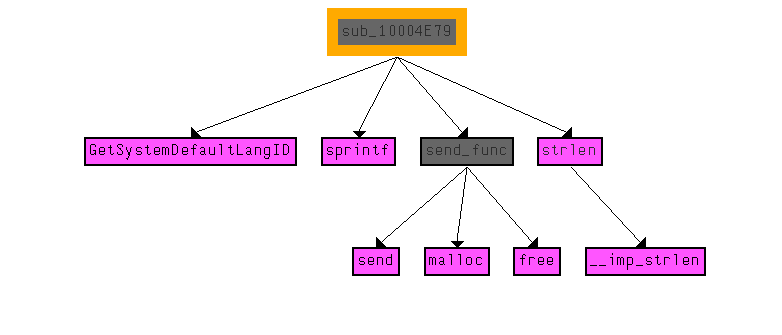
We can see that this function attempts to send the default language of the system throughout the network. - We have
strncpy,strlen,CreateThread,_strnicmpat a depth of 1, at depth 2, we have a variety of function calls that are related to networking, such assocket,recv, etc… - The program will sleep for 30 seconds exactly.
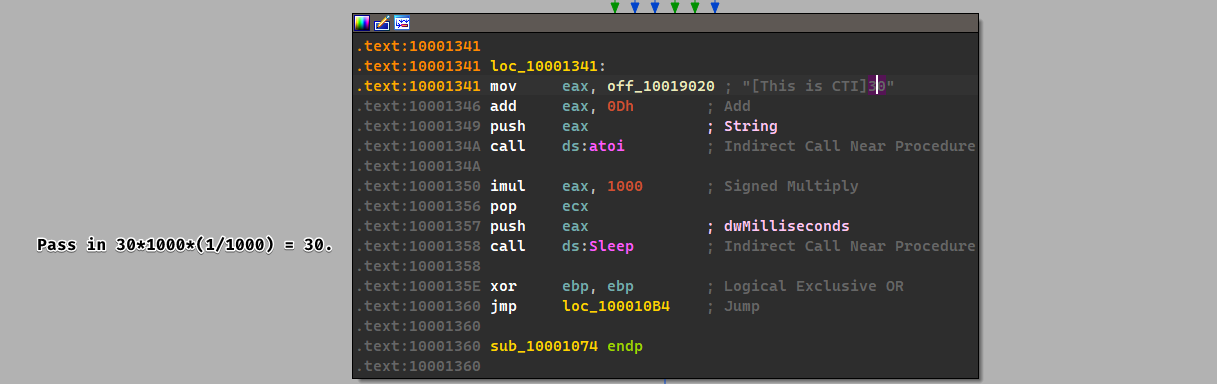
- The parameters were
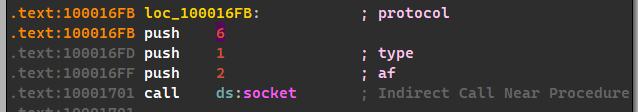
6,1and2respectively.
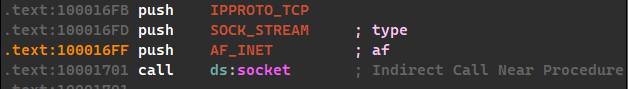
We used standard symbolic constants in order to view the constants this way.- Yes, the malware does use this:
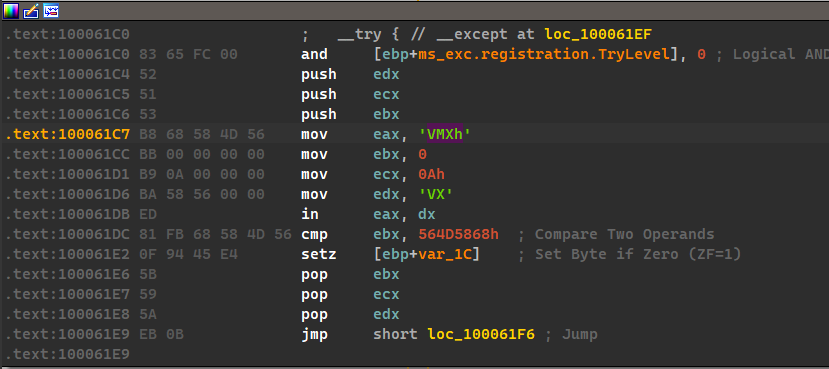
This seems to be the only occurrence of theininstruction, but the function that uses this instruction is called byInstallRT,InstallSAandInstallSB.
- We see random data.
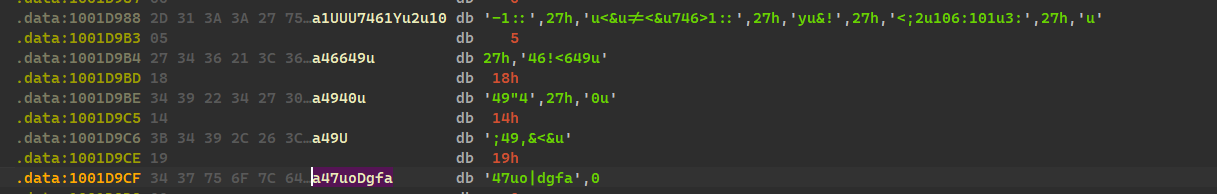
- We can see that this random data has been transformed to:
xdoor is this backdoor, string decoded for Practical Malware Analysis Lab :) 1234. - We transform it into a string by clicking A, which transforms it from bytes to ASCII string.
- It works by first grabbing the cursor’s location, then it iterates 0x50 times where: we obtain each byte, XOR it with 0x55 and patch each iteration with the newly XOR’d value.